Over the last few weeks I have discussed various ways to protect yourself and your computer from malicious users and software of different types both offline and online. Quite interestingly is the fact that there are so many types of computer attacks and the only way to stay secure is to abide by most of the basic security rules. A very interesting form of computer attack is the phishing attack. Phishing scams are one of the most popular forms of cybercrime, especially in Nigeria.
Phishing is a type of online identity theft in which fraudsters trick internet users into submitting personal information to illegitimate web sites. This may come in form of internet pop-ups, fraudulent websites and false emails. It usually tricks the victim into submitting sensitive information such as passwords and debit/credit card information. Usually, this information is gotten by sending you links that look like sites you can trust such as your banking provider or social networks and are able to steal your data as you enter it. Let’s look at an example of how a spoofed email is likely going to look like. Just yesterday, my friend, Samuel got this email from ‘Uber’.
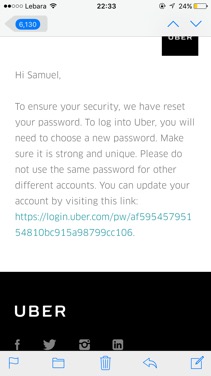
Apparently, Samuel actually has a Uber account and uses it very often. Ordinarily, anyone would have clicked that link since the email was properly crafted to look just like Uber’s email. This is a good example of a properly crafted phishing email.
How to Protect yourself against phishing
- Be suspicious of any emails asking for personal or confidential information especially information that is of a financial nature. Most legitimate organizations will not ask you to provide sensitive information via email and definitely not via popups too. Most banks will not even email you to ask for your information or to reset your internet banking passwords, etc.
- Don’t get pressured into providing sensitive emails. Just last week, as I shared on twitter, I got an email from “Mr Bill Gates” who wanted to give me the sum of $10,000,000 and needed me to fill out some information about myself and my bank within 3 days or lose the money. Most phishing attacks like to use the scare technique. “If you do not reset your password in 24 hours, your account will be deactivated and you will lose all the money you have kept in our bank. You signed it in the opening agreement.” Don’t allow yourself to be pressured into submitting your sensitive information, make sure you contact the merchant directly with the contact details originally provided by the merchant and obviously not the contact details in the email.
- Generic-looking emails are not for you. Most emails starting with “Dear Sir/Madam” and go ahead to ask for personal information are most likely fraudulent and phishing attempts. Some even come from banks or organizations where you don’t even have an account.
- Don’t ever submit confidential information via forms embedded within an email message. Everything you type in there will be remitted to the sender in plain text.
- Don’t connect to a website using links provided in an email. The phishing example I gave above is a perfect representation of this. Upon receiving that email, Samuel chose to reset his password directly from the Uber Website and this is what the real email looks like:
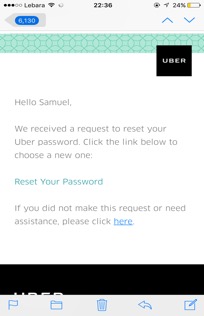
See how carefully crafted the phishing email is? Never use links in an email to connect to a website unless you are totally sure they are authentic. Type the URL directly into the address bar instead.
6. Just be sensible when it comes to phishing attacks. You can significantly reduce the chance of falling victim of a phishing attack simply by being sensible when online. Don’t download files or open attachment in emails or even social media unless you are absolutely sure it is authentic. Pay attention to shortened links, always place your mouse over a shortened link to see what the full address is before clicking it. Attackers use this very often. Don’t ever use public, unsecured Wi-Fi for banking, shopping or entering personal information online.
7. Maintain Effective software to combat phishing if you can afford one. Norton Internet Security for example, blocks fake websites automatically.
You should always be careful when giving out personal information over the internet. Keep an eye out for phishing schemes and never feel pressured to give up your personal information online. Also, always remember there is no African prince and Mr Bill Gates isn’t dashing you $10,000,000.
Joel Oseiga Aleburu is a Cyber Security Analyst and currently a researcher on Self Adaptive Privacy and Security . He is interested in encryption and vulnerabilities in general. Please feel free to send your questions to joelaleburu@gmail.com or contact him on Twitter: @joeloseiga
__________
Follow us on Twitter at @thesignalng
Copyright 2017 SIGNAL. Permission to use portions of this article is granted provided appropriate credits are given to www.signalng.com and other relevant sources.