The past three years have seen an increase in Fintech companies across African markets. Similarly, the past two years have also seen quite a number of cyber-attacks, the biggest being the WannaCry ransomware which has been described as the largest cyber-attack ever in history. In 2016 alone, more than 3 million credit card records were made public. There has never been a more critical time than now to take the security of systems and data more critically. Fintech companies literally have to ensure the confidentiality, integrity and availability of their systems and the data in their possession. Trust is the fuel on which Fintechs run. If your Fintech gets compromised once, gaining customer trust again will be extremely difficult.
In December last year, I was on a team that performed a code analysis and review for a new African Fintech start up. While it was pretty much evident that experienced full stack developers participated in the building of the project, there were still a good number of exploitable security flaws in the code and system design in general. Sometime early this year also, I had discovered a security design flaw in one of the major Fintech players in Africa’s market. Although I assume it has been fixed, It still brings to fore the need to be security conscious not only during and after the implementation of your system but also during the system design phase. While African Fintechs have been lucky not to have had any serious large scale cyber-attack over the years, it is important to avoid mistakes so that your application and start-up won’t break apart after the first cyber-attack it faces. Here are a few things to put into consideration.
- Have someone who actively knows about secure system development on your team.
Although appointing a Chief Information Security Officer in an organization is very important most especially if confidential data or critical systems are involved, it might be a little farfetched for me to recommend a start up that is probably managing the funds available to them to get a CISO. However, it is only reasonable if you have someone on your team who actively knows about secure system development and computer security. Have a Cyber Security personnel on your team. Building secure systems must be from the algorithm design. Attacks can happen at any point on any day. Although most African countries are sitting peacefully on the map.norsecorp.com cyber-attack map, this just might not last for long since more Fintech companies are bringing the African tech scene to the limelight. The
- System Architecture and Code and Review.
Before writing any code for your new Fintech application, the entire system architecture must be drawn out and the security requirements must be clearly set out and defined. Measures such as access control, system roles and privileges must be clearly defined and reviewed. This review must be done and sorted out before the coding begins. Your entire Fintech architecture should revolve around ensuring data privacy. Basic things such as mandating secure passwords, use of two factor authentication, etc. must be considered and clearly defined in the architecture design. It is very advisable to have someone who is knowledgeable in security and isn’t a part of the team do this review before coding begins.
Stop thinking about your system security as something you add and start thinking about it as a way you create your system. Review every line of code as many times as you can during the development. Ensure your engineers (or developers) follow best practices while writing the code and after your project is complete, review the code again for security loopholes.
- Go on an Encryption Spree.
Simply using SSL or HTTPS is just not enough. Every line of data should be encrypted. Complicate every line of code. Hash and encrypt all entries in your database. Encrypt every single layer of your system (or application). While in some instances, encryption might make your app slower, it totally depends on how this is done. People in security usually know about how to go around this. Methods such as server separation can come in really useful. Encryption helps in protecting the confidentiality of data which is one of the most important factors in Fintech due to the nature of sensitive costumer information that is usually handled. The last thing you want to happen is to wake up one morning and see all your customer data dumped on the internet. Attacks can come from anywhere at any time, the least you can do is to protect customer data and prevent attackers from gaining access to critical data.
- Access the Security of your Application/System.
Carry out penetration tests for your new application. Don’t be scared, pay white hackers to attempt a break into your system and point out the vulnerabilities exploited before you even launch the application. Also, it is good practice to carry out penetration testing every year and after every major change in your application. Your penetration tester can be either in-house or outsourced, it doesn’t really matter as far as they know their job. Also, fast and efficient bug fixing is the secret to having a secure organization. Fix bugs as soon as they are discovered.
- Carry out Risk Assessment and Mitigations.
The need for a risk assessment and mitigation framework cannot be overemphasized. Most start-ups generally don’t do this. They simply don’t care. Identify your critical assets and have a cyber risk calculation framework alongside a mitigation plan already in place. Managing internal risk is very important for Fintech companies. Always try to minimize risks while running your organization in general. Also, try as much as possible to align with industry standards such as the ISO/IEC 27000 for security management.
Ensuring the security of your system and protection of your data is a conscious and continuous process. It is really not so difficult if you start thinking about it from the very first day. While other types of attack such as social engineering still put your company at risk, the least you can do is to ensure the development of secure systems.
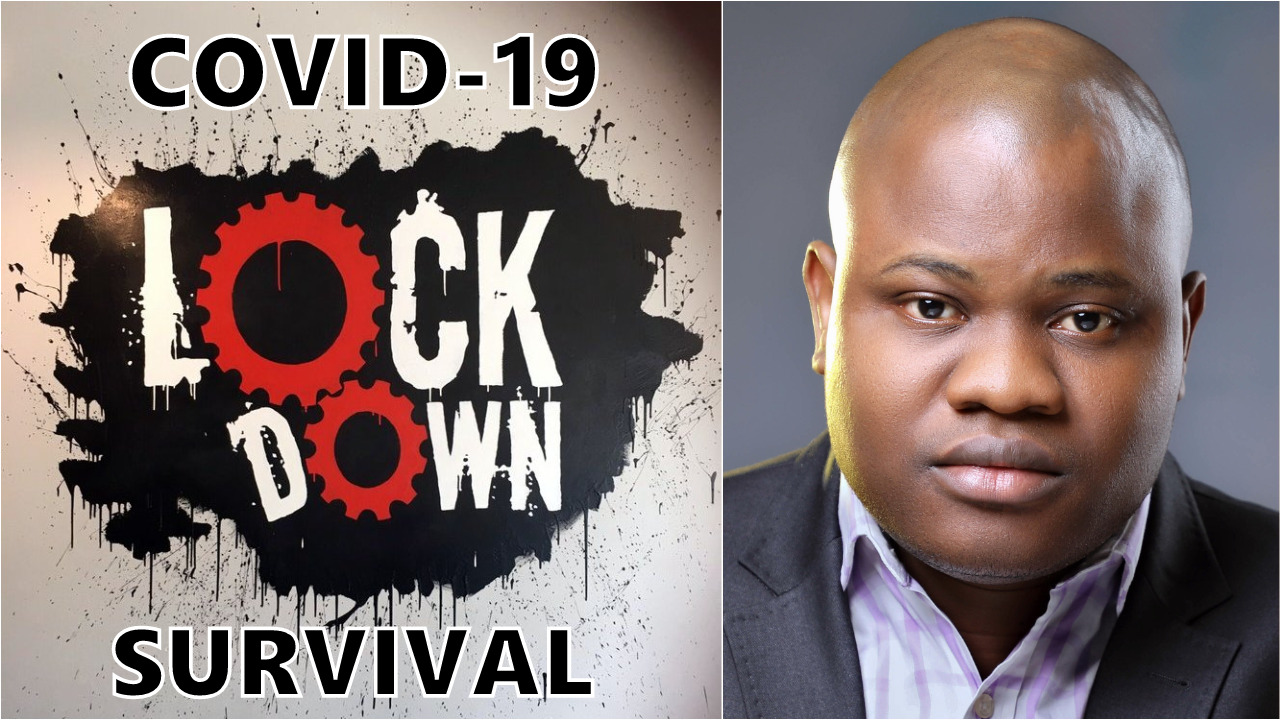
Joel Oseiga Aleburu is a Cyber Security Analyst and currently a researcher on Self Adaptive Privacy and Security . He is interested in encryption and vulnerabilities in general. Please feel free to send your questions to joelaleburu@gmail.com or contact him on Twitter: @joeloseiga
__________
Follow us on Twitter at @thesignalng
Copyright 2017 SIGNAL. Permission to use portions of this article is granted provided appropriate credits are given to www.signalng.com and other relevant sources.