Yesterday was a rather interesting day as news broke about another ransomware attack. The Petrwap ransomware that happened and caused significant damage to organizations in Ukraine and some other parts of the world. This came barely a month after the WannaCry ransomware attack affected the UK’s NHS before spreading further to infect computers in about 160 countries including Nigeria. If even after the WannaCry outbreak, your system was still affected by this Petrwap ransomware, then your patching capabilities and process is insufficient. Attackers are not moving slower. What fails you today, will surely fail you again in the future. Adapt or keep getting victimized over again. Before going further to discuss how to generally protect your systems from ransomware attacks, let us look at a few tips on the Petrwap ransomware attacks.
The Petrwap ransomware attack just like the WannaCry exploits a now patched vulnerability in Windows SMB. Unlike in WannaCry however, it also harvests admin credentials from infected systems, then uses standard windows administration tools such as WMIC and psexec to spread within an organisation. You can do the following:
- Patch your systems
- Disable SMBv1 (if you can)
- Save admin accounts for admin activities; stick to an unprivileged account for routine activities such as web browsing, email, etc.
- Keep Office and Adobe documents in protected/micro-disabled mode
This ransomware uses the existing EthernalBlue exploit that targets CVE-2017-0144 (check virus total for more information on this CVE) therefore patch it immediately with MS17-010.
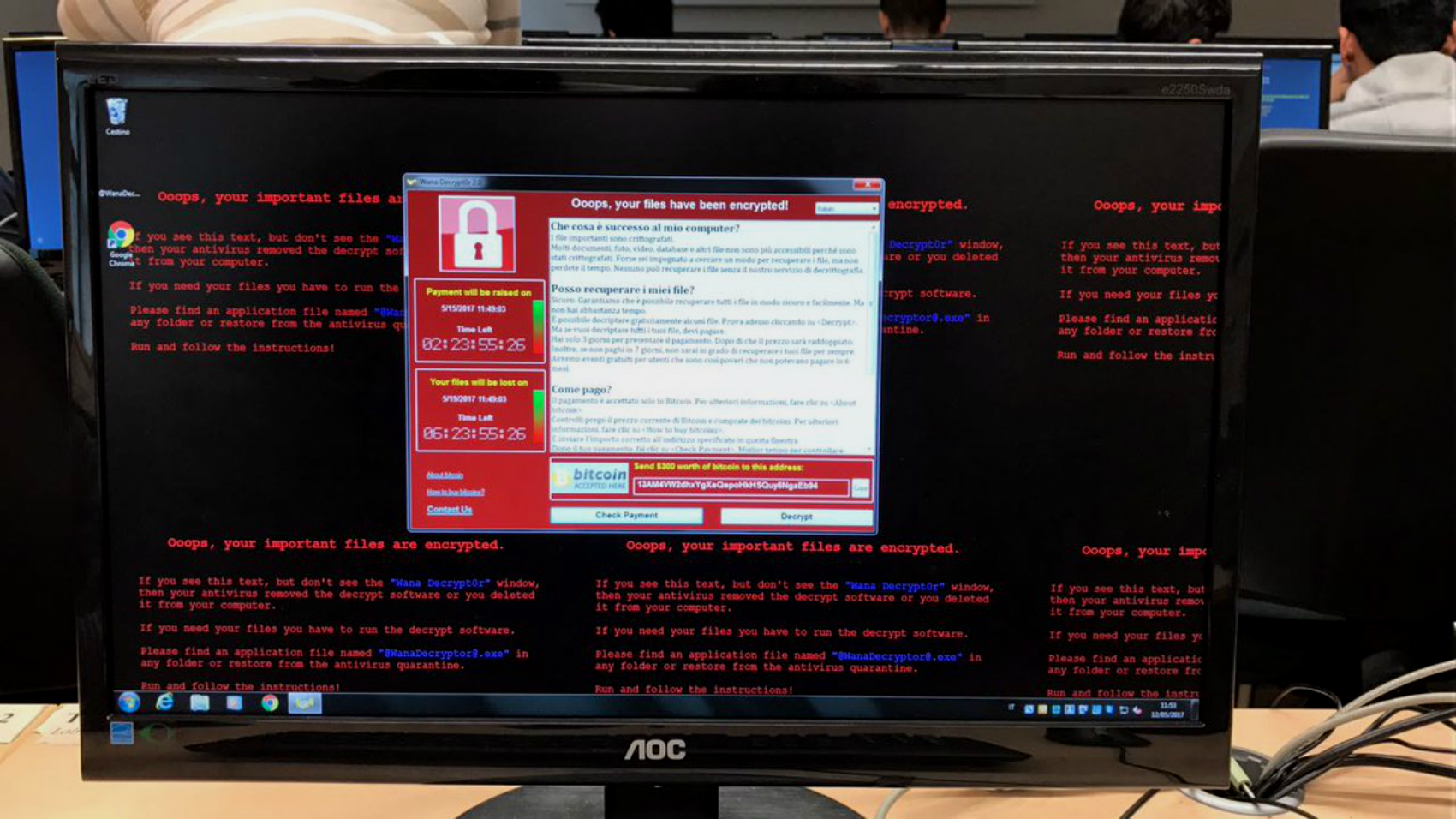
A ransomware is a very sophisticated type of computer malware worm that blocks a victim’s access to his/her files and on some occasions, spreads itself on the network. Generally, there are two broad types of ransomware:
- Encrypting ransomware: This could be really nasty. This type of ransomware uses quite advanced encryption algorithms and encrypts your files and access to them until a ransom payment is made for a decryption key to unlock the blocked files. Examples of this ransomware include Cryptolocker, Locky, CryptoWall among very many others.
- Screen Lockers: When screen lockers infect your computer, you get locked out of your operating system totally. This locks your system at start up stage so a user cannot access the desktop and any apps or files. Although the files the not get encrypted, the attackers still ask for a ransom before the affected computer can be unlocked. Examples of this include police-themed ransomware and Winlocker.
Some types of screen lockers infect the Master Boot Record (MBR) which is a section of a computer’s hard drive that allows the operating system to boot up. Whenever a ransomware attacks the MBR, the boot process won’t be able to complete as usual and a ransom request will be displayed on the screen. Examples include Satana and Petya.
Here are some ways to protect yourself from Ransomware attacks.
- Patch! Patch! Patch!: The very first step in ransomware prevention is to ensure your systems are patched up to date. Both WannaCry and Petrwap ransomware attacks took advantage of a vulnerabilities in Microsoft software. On both occasions, Microsoft had earlier released patches for the security loopholes and many people didn’t install the updates which left them open to attacks. Companies often release updates to fix vulnerabilities that can be exploited to install ransomware. It is just advisable to change your system settings to enable automatic updating in other to download the newest version and patch of a software and system as soon as available.
- Back up your files: The biggest damage suffered from a ransomware attack is the loss of files. A very good form of protection against this attack is to ensure you have a complete backup of your files on a totally different system. A good place to back up will be external drives that are not connected to the internet and are physically disconnected from your computers after backing up (otherwise they can be infected too). Backing up your files in the cloud is another option however, ensure the server has a high-level encryption and multi-factor authentication. This means that if you suffer an attack, you won’t lose any information to the hackers.
- Use a good (not free) antivirus program: Generally speaking, good and well updated anti-virus programs can detect and stop ransomware and most other types of malware from being downloaded onto computers and can even find it when it is. Most antivirus programs can scan files to see if they might contain ransomware before downloading them.
- Be suspicious of emails, websites and links: Most of the ransomware I analysed in 2016 were gotten from obscure porn sites and funny looking websites. Usually, before ransomware can work, hackers have to download malicious software onto a person’s computer. This is then used to launch the attack and encrypt files. The most common way to do this is through phishing emails, malicious adverts on websites and questionable programs. Phishing is the act of tricking people into handing over their card details or access to protected systems by sending emails that contain links or attachments that either takes you to a fake website that looks like the one you are familiar with or installs malware on your system. Exercise caution when opening unsolicited emails or visiting websites you are unfamiliar with.
- Never Pay the Ransom: It is advisable to never pay the ransom as it may not result in getting your files back. You can search the internet if there are already known keys or ways to unlock your computer from that ransomware if infected or just restore your device from your backup.
Social engineering is one of the most popular ways that computers are infected with ransomware. Try to stay updated about scams, phishing campaigns and suspicious websites. Most importantly, exercise common sense. If something seems too good to be true or suspicious, it probably is.
Joel Oseiga Aleburu is a Cyber Security Analyst and currently a researcher on Self Adaptive Privacy and Security . He is interested in encryption and vulnerabilities in general. Please feel free to send your questions to joelaleburu@gmail.com or contact him on Twitter: @joeloseiga
__________
Follow us on Twitter at @thesignalng
Copyright 2017 SIGNAL. Permission to use portions of this article is granted provided appropriate credits are given to www.signalng.com and other relevant sources.